OSPF on FreeBSD 11
Quagga's OSPF daemon provides dynamic routing for many operating systems. Here, I'll will demonstrate installing OSPF on FreeBSD 11 to advertise routes between hosts.
In my use case, each FreeBSD system hosts a few jails. Each jail is given its own /32 IP address on the loopback interface lo2. With OSPF, we can move jails between hosts in different locations and OSPF will advertise the host's IP route wherever the jail is running.
To start, here's a drawing of the configuration:
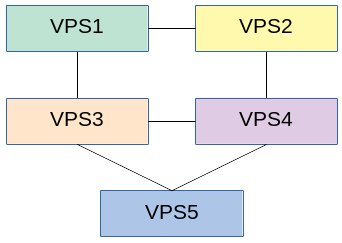
- VPS1 and VPS3 are in datacenter 1
- VPS2, 4 and 5 are in datacenter 2.
- We want the traffic between hosts in the same datacenter at a lower cost than the traffic that traverses between datacenters.
-
Installing Quagga's OSPFd on FreeBSD is as easy as
pkg install quagga. -
Next, you'll need to enable IP routing.
Addnet.inet.ip.forwarding=1 in /etc/sysctl.confto /etc/sysctl.conf and usesysctl net.inet.ip.forwarding=1 in /etc/sysctl.confto make the change without needing to reboot. -
Add Quagga to your
/etc/rc.conf.localfile:sysrc -f /etc/rc.conf.local quagga_enable="YES" sysrc -f /etc/rc.conf.local quagga_flags="-A 127.0.0.1" sysrc -f /etc/rc.conf.local quagga_daemons="zebra ospfd" -
Create the zebra.conf file:
vim /usr/local/etc/quagga/zebra.conf
and add these two lines (replacing the hostname and password):hostname <your hostname> password <your password> -
Create the ospfd.conf file (replacing the hostname, password, and keys):
vim /usr/local/etc/quagga/ospfd.conf
Using the following configuation, VPS1 will favor the link to VPS3 using VPS2 as a secondary path when routing to VPS4. The samecost 11is defined on VPS4 towards the link to VPS3 to ensure asymmetric routing does not occur.! hostname <your hostname> password <your password> ! ! ! interface tap2 description TAP to VPS2 ip ospf network point-to-point ip ospf authentication ip ospf authentication-key <your key> ip ospf cost 11 ! interface tap3 description TAP to VPS3 ip ospf network point-to-point ip ospf authentication ip ospf authentication-key <your key> ! router ospf ospf router-id 0.0.0.1 passive-interface default no passive-interface tap2 no passive-interface tap3 network 10.8.0.0/24 area 0.0.0.0 network 172.16.0.0/24 area 0.0.0.0 area 0.0.0.0 authentication ! line vty ! end



